
Speed, key size, and security tradeoffs across the major algorithm families.

Three concepts that are frequently confused — each serves a distinct purpose in modern systems.
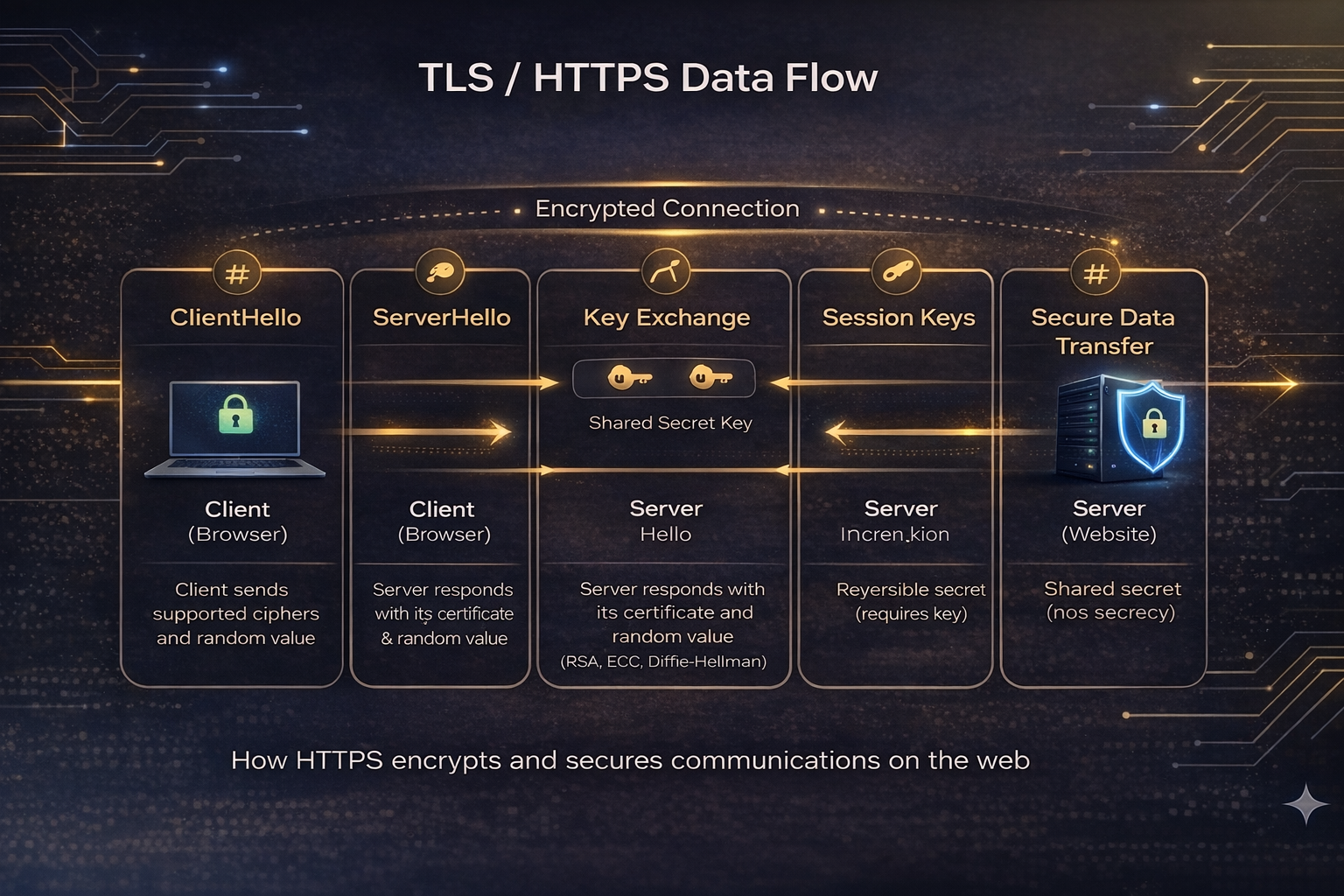
Cryptography in action — how the algorithms on this site combine to secure every HTTPS connection.
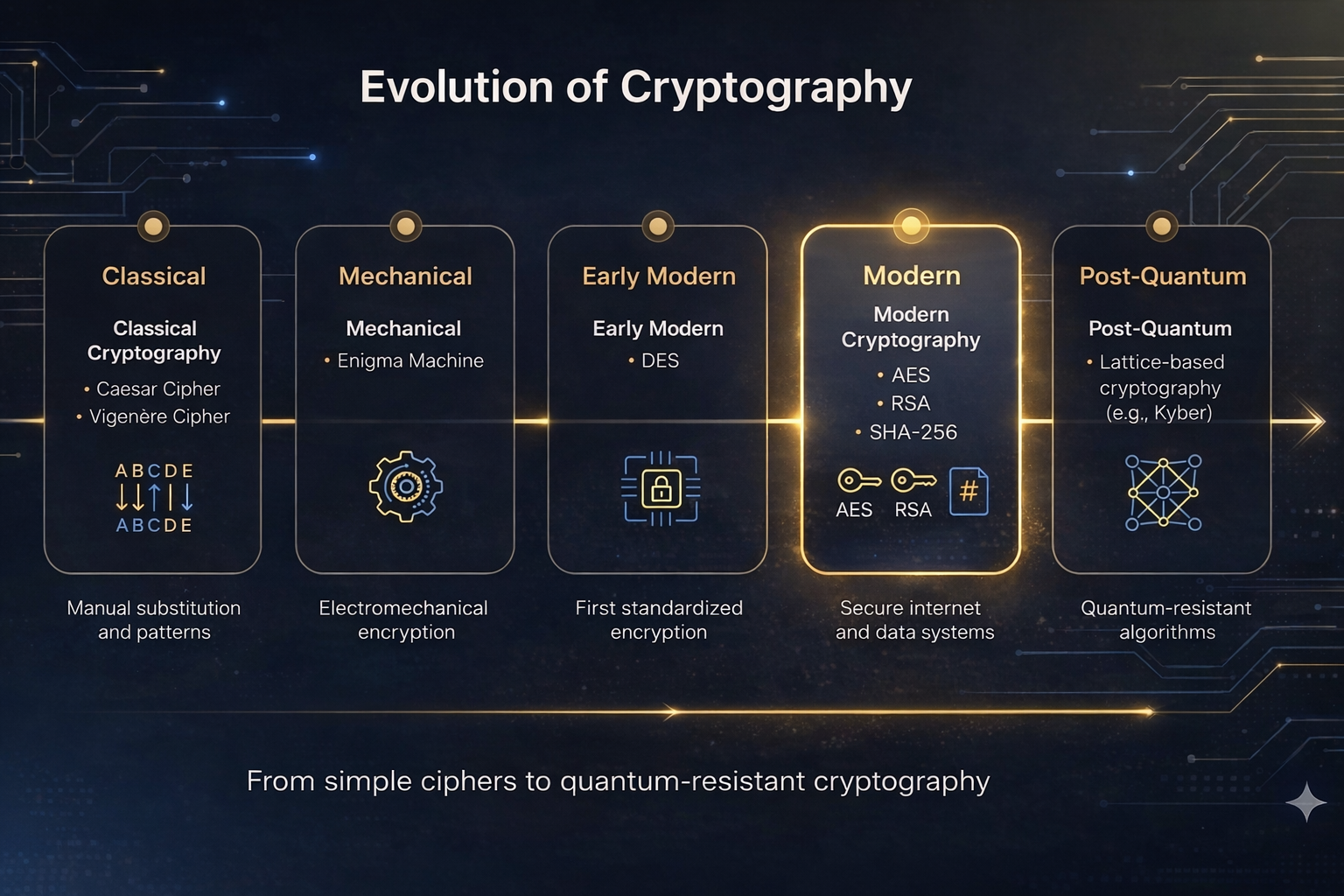
From Caesar ciphers to post-quantum standards — the history of the field at a glance.